Analyze Smart Contracts at Scale —
Across All Execution Paths
Static, dynamic, semantic, and infrastructure vulnerability detection for EVM smart contracts.
Vulnerability Detection results require a subscription.
Static, Dynamic, Semantic & Infrastructure Risk Analysis
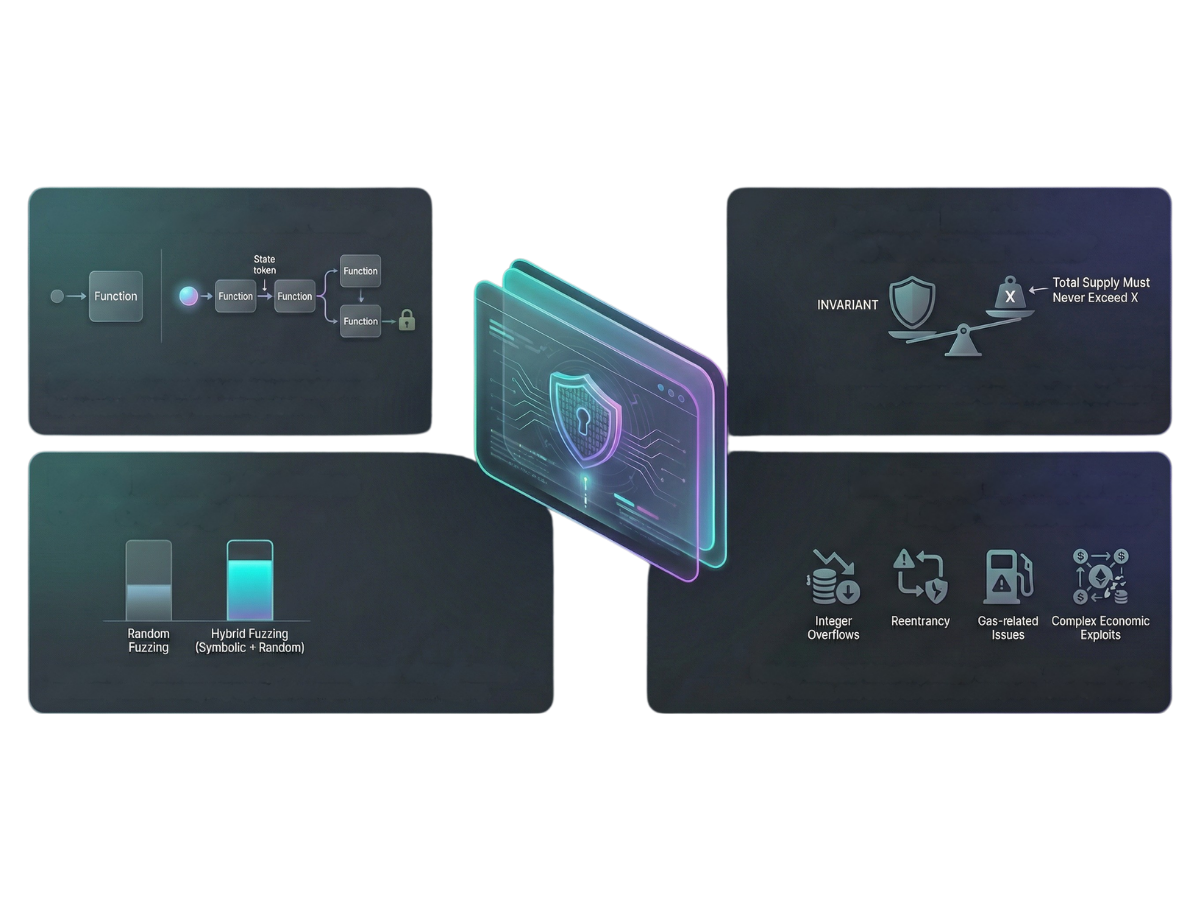
Dedaub's Vulnerability Detection combines static analysis, dynamic analysis (fuzzing), LLM-assisted semantic similarity, and hack-related infrastructure scoring to identify vulnerabilities in EVM smart contracts. More than 100 proprietary static analysis algorithms evaluate control flow, storage behavior, and value flows across execution paths to surface concrete warning classes. Contracts flagged by static analysis are automatically fuzzed to determine whether a warning can lead to fund loss. LLM-assisted "Find Similar" detects structurally or logically equivalent functions across contracts, while Hack-Related Proximity Scoring measures interaction-based similarity to known malicious infrastructure through relationship graph analysis.
Hack-Related Proximity Scoring
Hack-related proximity scoring introduces a graph-based risk signal that measures how closely an address is related to known malicious infrastructure.
Find Similar (Semantic Contract Matching)
Find Similar uses LLM-assisted semantic analysis on decompiled contracts to identify other contracts implementing structurally or logically similar functions — even when bytecode, constants, or compiler settings differ. Instead of relying on hash matching, it compares normalized control-flow and behavioral structure to detect rewritten clones, modified exploit templates, and function-level logic reuse across deployments. This enables researchers to determine whether a vulnerability is isolated or shared across a broader contract family.
Contract Filters
Dedaub's Contract Library offers a robust search interface for filtering contracts based on various criteria. You can refine your search by specific vulnerability warnings, contract states, or lists of saved contracts.

Vulnerability Coverage
Accessible selfdestruct, reentrancy (including read-only variants), flashloan callback misuse, permit omissions, tainted call chains, DoS patterns, swap reachability, cryptographic misuse, and 100+ additional warning classes — continuously expanded as new attack vectors emerge.

Dynamic Analysis (Fuzzing)
In the Dedaub model, dynamic analysis is implemented through automated fuzzing. Contracts flagged by static analysis are automatically exercised with generated transaction inputs to determine whether a vulnerability can lead to fund loss. Findings such as FUZZED: Fund Loss, FUZZED: Arbitrary Call, or FUZZED: Selfdestruct indicate that a warning has been dynamically validated.
API & Integration
Create Your Free Account Now
Security Suite LoginAre you looking for security audits? Find out more here.