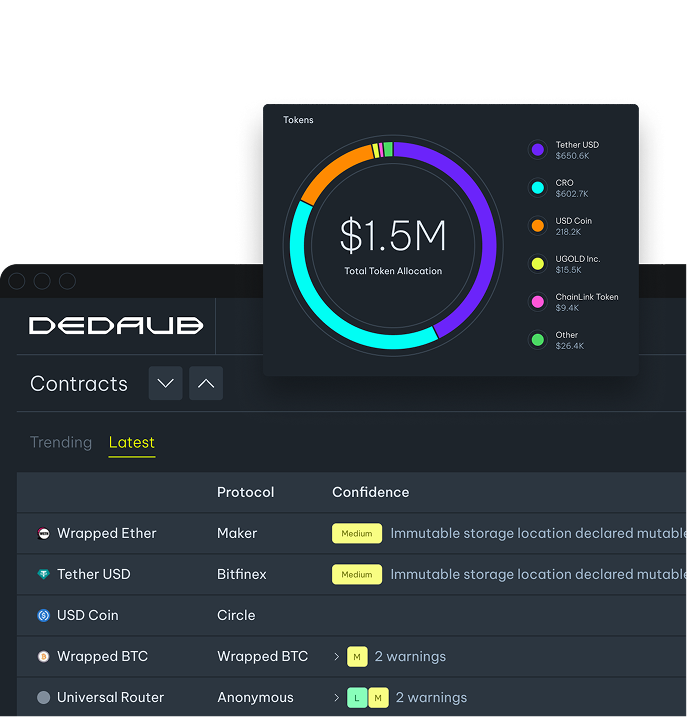
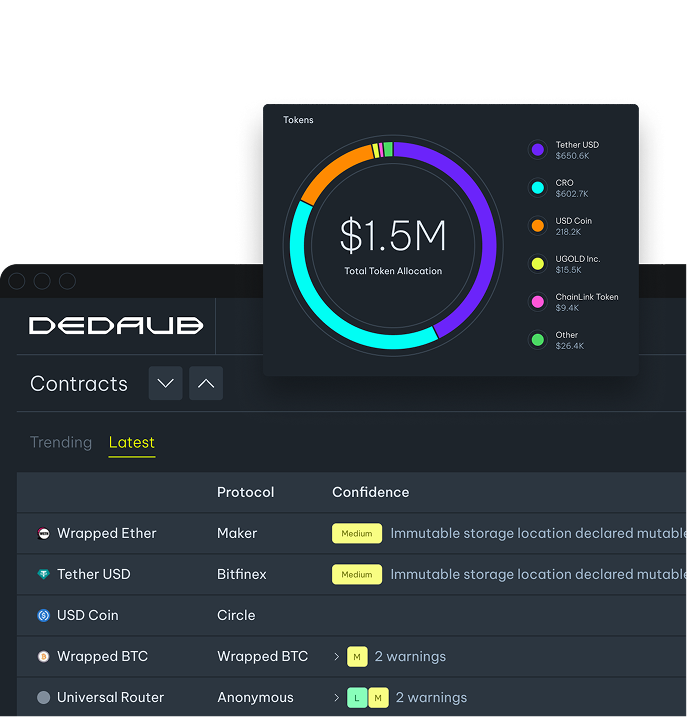
Your Protocol's Logic. Our Security Experts Watching It.
Custom agents · Multi-chain · Protocol-level granularity

Proactive Threat Detection
Identify pre-attack signals — abnormal state changes, suspicious deployment patterns, and emerging exploit sequences — by continuously analyzing structured onchain data before threats reach your protocol.
Powered by Security Suite Intelligence
Every monitored contract is automatically decompiled and assessed through static analysis, dynamic fuzzing, LLM-assisted semantic similarity, and hack-related infrastructure scoring — giving your Monitoring rules a deep structural understanding of the code they protect.
Multi-Chain Coverage
Monitor contract activity, high-value transfers, and protocol behavior across every EVM chain Dedaub indexes — including Ethereum, Arbitrum, Optimism, Base, Binance, Polygon, and Avalanche.
Real-Time Alerts and Triggers
Receive notifications via email or webhook when a monitoring rule fires — enabling your team to respond to large transfers, governance changes, or suspicious interactions shortly after they occur.
Expert-Written Monitoring Rules
Dedaub engineers build and maintain Monitoring queries tailored to your protocol's specific contracts, risk model, and operational logic — not generic templates.
Full-Spectrum Protocol Oversight
Track governance proposals, transaction integrity, contract state changes, and known attack vectors in a single Monitoring layer — built on the same intelligence used by Dedaub's audit and research teams.
Proactive Threat Detection
Identify pre-attack signals — abnormal state changes, suspicious deployment patterns, and emerging exploit sequences — by continuously analyzing structured onchain data before threats reach your protocol.
Powered by Security Suite Intelligence
Every monitored contract is automatically decompiled and assessed through static analysis, dynamic fuzzing, LLM-assisted semantic similarity, and hack-related infrastructure scoring — giving your Monitoring rules a deep structural understanding of the code they protect.
Multi-Chain Coverage
Monitor contract activity, high-value transfers, and protocol behavior across every EVM chain Dedaub indexes — including Ethereum, Arbitrum, Optimism, Base, Binance, Polygon, and Avalanche.
Real-Time Alerts and Triggers
Receive notifications via email or webhook when a monitoring rule fires — enabling your team to respond to large transfers, governance changes, or suspicious interactions shortly after they occur.
Expert-Written Monitoring Rules
Dedaub engineers build and maintain Monitoring queries tailored to your protocol's specific contracts, risk model, and operational logic — not generic templates.
Full-Spectrum Protocol Oversight
Track governance proposals, transaction integrity, contract state changes, and known attack vectors in a single Monitoring layer — built on the same intelligence used by Dedaub's audit and research teams.
How It Works
The DedaubQL Language
Write monitoring agents in DedaubQL — SQL extended with gadgets for table access, contract lookups and eth_call expressions.
Decoded Transaction Data
Agents operate on decoded block, transaction, log and token-ledger data. Extract decoded calldata, returndata and event parameters without writing your own decoders.
Multi-Network & Parameterized
Use the params gadget to define per-network values and loop over networks to run the same logic across chains.
Configurable Scheduling
Schedule agents to run every few minutes or at longer intervals. Each run processes only the new blocks since the last execution.
Incremental Materialized Views
Build materialized views that update incrementally as new blocks arrive — no full-table rescans, constant-time processing per block.
Webhook and Email Delivery
Configure alerts per agent with unique-key deduplication. Each result row triggers at most one notification per key, eliminating duplicate alerts across runs.
Turn Security Logic into Live Monitoring
Detect Whale Movements
Large, unexpected token movements can signal exploits, insider activity, or market manipulation. This agent flags transfers above a value threshold using the token_ledger gadget.
- ● token_ledger gadget records credits and debits for every token movement
- ● Filter on value thresholds to surface only significant transfers
- ● tx_hash() computes the transaction hash from block number and index
Set the unique key to the transaction hash so each transaction triggers at most one alert. Schedule the agent at sub-minute intervals to continuously scan new blocks.
Catch Protocol Drains Early
A single transaction draining millions from a protocol is often the first sign of an exploit. This agent calculates net value moved per transaction, filtering out noise to surface only significant drains.
- ● Use the ref gadget to join token_ledger to a materialized contracts list
- ● Group by transaction to sum all transfers in and out
- ● HAVING clause filters out small net flows, alerting only on large drains
Set the unique key to the transaction hash to receive a single alert per drain event. The aggregate reflects net outflow since token_ledger records both debits and credits.
Flag Unknown Governance Activity
New governance participants submitting proposals can indicate legitimate community growth — or a governance attack. This agent tracks first-time callers so your team can review before a vote begins.
- ● transaction_detail gadget decodes calldata and returndata for each function call
- ● from_a field identifies the transaction sender
- ● Filter by contract address and function signature
Set the unique key to the caller address. Use a one-time back-fill so historical callers are recorded — after that, only new callers generate alerts.
Dedaub Monitoring Workshop
A hands-on walkthrough of building monitoring agents with DedaubQL — from writing your first query to deploying a live agent with schedules, unique keys, and backfilling. Three real examples, zero boilerplate.
$Billions secured in TVL through proactive blockchain security measures
Why Dedaub?
$3M
IN BUG BOUNTIES IN 11 SUCCESSFUL CLAIMS FOR IDENTIFYING CRITICAL ISSUES
$Billions
IN TVL SECURED VIA PROACTIVE WHITE-HAT HACKING and SEAL 911 WAR ROOMS
200+
SMART CONTRACT SECURITY AUDITS FOR LEADING DEFI PROTOCOLS
Trusted
Trusted by security teams at leading DeFi protocols and Web3 companies globally for reliable protocol monitoring.
Expertise
Leverage years of smart contract security expertise and cutting-edge static analysis technology.
Knowledge
Access comprehensive threat intelligence and security insights from industry-leading blockchain security researchers.
Designed by World-Leading Security Experts
 CHAINLINK BUILD PROGRAM PARTNERSHIP
CHAINLINK BUILD PROGRAM PARTNERSHIP ARBITRUM DAO SECURITY ADVISOR
ARBITRUM DAO SECURITY ADVISOR OASIS PROTOCOL SAPPHIRE'S SECURITY PARTNER
OASIS PROTOCOL SAPPHIRE'S SECURITY PARTNER FOUNDING COLLABORATOR OF THE SEAL 911
FOUNDING COLLABORATOR OF THE SEAL 911 UNISWAP FOUNDATION SECURITY SECURITY PROVIDER
UNISWAP FOUNDATION SECURITY SECURITY PROVIDER MEMBER OF ZKSYNC SECURITY COUNCIL
MEMBER OF ZKSYNC SECURITY COUNCILDesigned by World-Leading Security Experts
 CHAINLINK BUILD PROGRAM PARTNERSHIP
CHAINLINK BUILD PROGRAM PARTNERSHIP ARBITRUM DAO SECURITY ADVISOR
ARBITRUM DAO SECURITY ADVISOR OASIS PROTOCOL SAPPHIRE'S SECURITY PARTNER
OASIS PROTOCOL SAPPHIRE'S SECURITY PARTNER FOUNDING COLLABORATOR OF THE SEAL 911
FOUNDING COLLABORATOR OF THE SEAL 911 UNISWAP FOUNDATION SECURITY SECURITY PROVIDER
UNISWAP FOUNDATION SECURITY SECURITY PROVIDER MEMBER OF ZKSYNC SECURITY COUNCIL
MEMBER OF ZKSYNC SECURITY COUNCILReal-Time Defense, Designed for You
Real-Time Defense, Designed for You